20 Excellent Pieces Of Advice For Deciding On Shielded Websites
Wiki Article
"Zk Power Shield." What Zk Snarks Protect Your Ip And Your Identity From The World
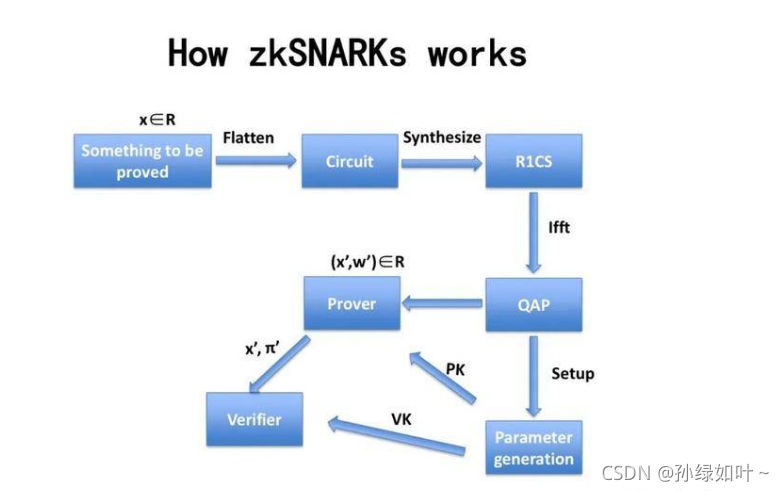
The privacy tools of the past were based on a notion of "hiding among the noise." VPNs connect you to another server; Tor moves you through nodes. While they are useful, the main purpose is to conceal your source of information by moving it away, and not by convincing you that it doesn't need to be revealed. Zk-SNARKs (Zero-Knowledge Short Non-Interactive Arguments of Knowledge) introduce a distinct paradigm that can prove you are authorized to take an action, by not revealing who you are. In ZText, that you broadcast a message in the BitcoinZ blockchain. The network will verify that you're legitimately participating with an authentic shielded account, however it's not able to identify which individual address it was that broadcasted to. Your IP address, the identity of you being part of the transaction becomes unknowable to the viewer, but confirmed to the protocol.
1. The end of the Sender -Recipient Link
In traditional messaging, despite encryption, makes it clear that there is a connection. The observer is able to see "Alice has been talking to Bob." Zk-SNARKs make this connection impossible. When Z-Text broadcasts a shielded transaction and the zk-proof is a confirmation that this transaction is legal--that the sender's account is balanced and that the keys are valid--without divulging that address nor recipient's address. To an outside observer, it is seen as a security-related noise that comes in the context of the network itself and in contrast to any one particular participant. A connection between two distinct human beings is then computationally impossible establish.
2. IP Protecting IP addresses at the Protocol Level, but not at the Application Level.
VPNs as well as Tor protect your IP as they direct traffic through intermediaries. However, those intermediaries create new points for trust. Z-Text's use of zk-SNARKs means your personal information is not crucial to the transaction verification. When you transmit your secured message on the BitcoinZ peer-to'-peer community, you belong to a large number of nodes. The ZK-proof makes sure that observers observe the networks traffic, they are not able relate the text message that is received and the wallet or account that is the originator, as the certificate doesn't hold that information. The IP's information is irrelevant.
3. The Elimination of the "Viewing Key" Dialogue
For many privacy and blockchain systems they have"viewing keys" or "viewing key" that allows you to decrypt transaction details. Zk's-SNARKs which are implemented within Zcash's Sapling protocol and Z-Text, permit selective disclosure. You are able to demonstrate that you sent a message with no divulging your IP or the transactions you made, or even the whole content of that message. The evidence itself is only being shared. This granular control is impossible for IP-based systems since revealing this message will reveal the sources of the.
4. Mathematical Anonymity Sets That Scale Globally
In a mixing system or a VPN that you use, your privacy is restrained to only the other people who are in the pool at that specific time. With zk-SNARKs, your anonymity set is every shielded address to the BitcoinZ blockchain. Because the verification proves the sender is a shielded address in the millions of others, and does not give any suggestion of which one. Your protection is shared across the entire network. You are hidden not in a small room of peers or in a global gathering of cryptographic IDs.
5. Resistance to Attacks on Traffic Analysis and Timing Attacks
These sophisticated adversaries don't just browse IPs; they analyze patterns of traffic. They analyze who is sending data, when and how they correlate to the exact timing. Z-Text's use with zk SNARKs when combined with a Blockchain mempool can allow for the dissociation of operation from broadcast. It's possible to construct a blockchain proof offline, and then broadcast it later for a node to transmit the proof. When you broadcast a proof, the time it was made for its inclusion in a block is not reliably correlated with the moment you constructed it, breaking the timing analysis process that frequently will defeat the simpler anonymity tools.
6. Quantum Resistance Utilizing Hidden Keys
They are not quantum resistant. However, if an attacker could track your online activity now in the future and then crack your encryption, they can link your IP address to them. Zk-SNARKs, as used within Z-Text are able to protect the keys you use. Your public key is never displayed on blockchains as the proof proves that you're using the correct key and does not show the key. The quantum computer, to the day, could just see proofs, however, not the keys. Past communications remain secret because the keys used to be used to sign them was never revealed for cracking.
7. Inexplicably linked identities across multiple conversations
With just a single wallet seed, you can generate multiple shielded addresses. Zk SNARKs will allow you to prove that you are the owner of one account without knowing which. You can therefore have more than ten conversations, with ten other people. However, no participant, not even the blockchain itself, will be able to be able to link these conversations back to the similar wallet seed. The social graph of your network is mathematically split by design.
8. The removal of Metadata as an Attack Surface
Many regulators and spies say "we aren't requiring the content or the metadata." It is true that IP addresses represent metadata. People you contact are metadata. Zk's SNARKs have a uniqueness among privacy options because they block metadata within the cryptographic layers. They do not include "from" or "to" fields that are plaintext. There's no metadata for make a subpoena. Only the proof, and the proof can only prove that a legal event occurred, and not who.
9. Trustless Broadcasting Through the P2P Network
When using a VPN you are able to trust the VPN provider not to track. If you are using Tor as a VPN, you trust that this exit node will not observe. Through Z-Text's service, you transmit your zk-proofed transaction BitcoinZ peer network. Connect to a handful of random nodes and send an email, and then leave. These nodes will not gain any knowledge since the evidence doesn't reveal anything. They can't even know if you're the source as you might be sharing information for someone else. The internet becomes a trustworthy service for private data.
10. "The Philosophical Leap: Privacy Without Obfuscation
They also mark one of the most philosophical transitions in the direction of "hiding" towards "proving there is no need to reveal." Obfuscation technology acknowledges that truth (your ID, IP) could be harmful and should be kept hidden. Zk-SNARKs acknowledge that the truth isn't important. All the protocol has to do is understand that you're authenticated. This transition from hiding your identity to active inevitability is central to the ZK-powered shield. Your IP and identification are not concealed. They only serve to enhance the purpose of the network thus they're never needed to be transmitted or disclosed. View the top shielded for website examples including encrypted text app, encrypted text message, messenger private, encrypted text app, encrypted messaging app, encrypted in messenger, messages in messenger, messages in messenger, encrypted text, encrypted in messenger and more.
Quantum-Proofing Your Chats : Why Zk And Zaddresses Are Resisting Future Encryption
The threat of quantum computing is frequently discussed as a boogeyman for the future that will break all encryption. In reality, it is complicated and pressing. Shor's method, when ran with a sufficient quantum computing device, could break the elliptic curve cryptography system that protects the majority of internet and even blockchain. There is a risk that not all cryptographic algorithms are inherently secure. ZText's architectural framework, based off Zcash's Sapling protocol as well zk's SNARKs is a unique system that thwarts quantum encryption in ways traditional encryption doesn't. The trick is in determining what will be revealed as opposed to what's secret. by ensuring that the public passwords remain private on the Blockchain Z-Text secures something for quantum computers in order to sabotage. Your old conversations, identity and wallet will remain protected not by the complexity of it all, but rather by invisible mathematics.
1. The Fundamental Vulnerability: Exposed Public Keys
To fully understand why ZText is quantum resistant, first realize why many systems not. With standard blockchain transactions the public key you have is released at the time you purchase funds. Quantum computers are able to access the publicly exposed key and through Shor's algorithm extract your private keys. Z-Text's shielded transaction, using an address called z-addresses don't reveal to the public key. Zk-SNARK confirms that you hold this key without having to reveal it. The public key is private, giving the quantum computer no way to penetrate.
2. Zero-Knowledge Proofs as Information Minimalism
The zk-SNARKs inherently resist quantum because they use the difficulty in solving problems that are not so easily solved with quantum algorithms as factoring, or discrete logarithms. The most important thing is that the actual proof provides zero detail about the key witness (your private secret key). Even if a quantum computer might theoretically defy the underlying assumption of the proof it would have nothing for it to operate with. The proof is a cryptographic dead end that checks a statement but does not contain details about the statements' content.
3. Shielded Addresses (z-addresses) as obscured existence
A z-address within Z-Text's Zcash protocol (used by Z-Text) will never be recorded via the blockchain any way linking it to transaction. When you receive funds or messages, the blockchain shows that a shielded pool transaction was made. Your exact address is concealed among the merkle-like tree of notes. A quantum computer scanning the blockchain scans for only trees and evidences, not leaves or keys. Your cryptographic address is there, however it is not visible to the eye, which makes its existence invisible to retrospective examination.
4. "Harvest Now, Decrypt Later" Defense "Harvest Now, Decrypt Later" Defense
The largest quantum threat in the present is not an active attack, but passive collection. Cybercriminals can grab encrypted information from the internet. They can then archive them, and then wait for quantum computers' maturation. In the case of Z-Text An adversary is able to search the blockchain for information and obtain all the shielded transactions. The problem is that without the view keys and never having access to public keys, they will have an insufficient amount of data to decrypt. The data they acquire is made up of proofs with no knowledge which, in the end, will not have encrypted messages which they may later break. The message is not encrypted in the proof. What is encrypted in the evidence is merely the message.
5. Important to use only one-time of Keys
Many cryptographic systems allow using a key over and over again creates visible data that can be analysed. Z-Text, built on the BitcoinZ blockchain's implementation of Sapling is a system that encourages the acceptance of various addresses. Each transaction may use an illegitimate, unique address created from the same seed. It means that even if one address were somehow damaged (by an unquantum method), the others remain in good hands. Quantum resistance is increased by that constant rotation of the keys which reduces the effectiveness each cracked key.
6. Post-Quantum Inferences in zk.SNARKs
Modern zk-SNARKs typically rely on combination of curves with elliptic curvatures, which are theoretically insecure to quantum computers. But, the particular construction used in Zcash and Z-Text has been designed to be migration-ready. It was developed to be able to later support post quantum secure zk-SNARKs. As the keys will never be exposed, transitioning to a modern proving mechanism can occur by addressing the protocol and not forcing users to reveal their information about their. The shielded pool design is advanced-compatible with quantum-resistant cryptography.
7. Wallet Seeds and the BIP-39 Standard
Your wallet seed (the 24 characters) isn't quantum vulnerable in the same manner. The seed is basically a very large random number. Quantum computers aren't much superior at brute-forcing random 256-bit numbers than classical computers due to the limits of Grover's algorithm. The issue lies with the derivation of public keys from the seed. By keeping those public keys from being discovered by using zk_SNARKs, the seed is secure even within a postquantum universe.
8. Quantum-Decrypted Metadata. Shielded Metadata
While quantum computers might cause problems with encryption however, they will still have to deal with issues with Z-Text's inability to conceal metadata at the protocol level. A quantum computer might be able to tell you that an exchange that occurred between two participants if they had their public keys. If those keys were not disclosed then the transaction becomes one-way proof of zero knowledge that doesn't include any information on the address of the transaction, the quantum machine can see only the fact that "something transpired in the shielded pool." The social graph, the time as well as the frequency remain undiscovered.
9. Merkle Tree as a Time Capsule. Merkle Tree as a Time Capsule
Z-Text stores the messages stored in the merkle tree in blockchain's protected notes. The structure itself is resistant quantization because, it is difficult to pinpoint a specific note it is necessary to know the note's commitment to the note and where it is in the tree. Without a view key quantum computers are unable to differentiate it from the millions more in the tree. The effort required to searching the entire tree for one specific note is quite significant, even for quantum computers, and grows each time a block is added.
10. Future-proofing Using Cryptographic Agility
One of the main feature of Z-Text's quantum resistivity is the cryptographic agility. Since the platform is based upon a blockchain-based protocol (BitcoinZ) that is able to be developed through consensus by the community cryptographic protocols can be removed as quantum threats materialize. Customers aren't bound by any one particular algorithm forever. Because their past is hidden and the keys are auto-custodianized, they can move to new quantum-resistant curves while not revealing their previous. This architecture will ensure that your messages are secured not just in the face of threats today, however, against threats from tomorrow as well.
